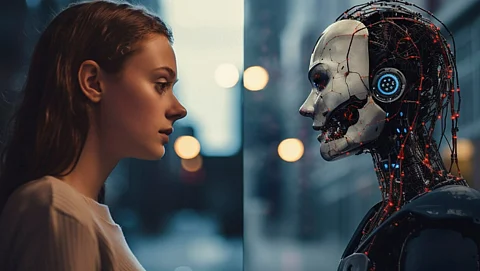
URGENT UPDATE: Cybercriminals are leveraging AI to unleash cloud attacks faster than ever, targeting vulnerabilities in third-party software. A new report from Google Cloud Security reveals that the time between vulnerability disclosure and exploitation has dramatically shrunk, posing a critical threat to businesses relying on cloud infrastructure.
This alarming trend shows that the window for attackers has collapsed from weeks to mere days, according to the report based on observations from the second half of 2025. The findings underscore an urgent need for businesses to adopt automated, AI-powered defenses to keep pace with this escalating cyber threat.
The report highlights that most attacks are now directed at unpatched vulnerabilities in popular third-party applications rather than core infrastructure like Google Cloud or Amazon Web Services (AWS). Cybercriminals, including organized gangs and state-sponsored actors like UNC4899 from North Korea, are exploiting these weaknesses with unprecedented efficiency.
One striking example involved a critical remote code execution (RCE) vulnerability in React Server Components, a widely used JavaScript library. Attacks on this vulnerability began within 48 hours of its public disclosure, indicating a concerning shift in attacker tactics. Another incident involved the exploitation of an RCE vulnerability in the XWiki Platform, where attackers gained access to systems just months after a patch was made available.
Furthermore, the report reveals that attackers are increasingly sophisticated, using social engineering tactics such as voice-based phishing (vishing) and exploiting trusted relationships with third parties. In fact, 17% of attacks involved vishing, while 21% leveraged compromised identities, signaling a dangerous evolution in cybercrime strategies.
What’s particularly troubling is that 45% of intrusions resulted in data theft without immediate extortion attempts. This stealthy approach allows attackers to remain undetected for extended periods, making it even more critical for businesses to have robust incident response plans in place.
To combat these threats, the report stresses the necessity for organizations to enhance their security measures. Recommendations include ensuring all software, especially third-party applications, is automatically updated, strengthening identity and access management systems, and closely monitoring network activity for unusual behaviors.
Small and medium-sized enterprises are particularly vulnerable, lacking the resources to combat these sophisticated attacks. Experts advise these businesses to consider managed service providers with the expertise needed to implement effective cybersecurity measures.
As the digital landscape evolves, the stakes have never been higher. The urgency to act is now. Businesses must prioritize cybersecurity to defend against these rapidly evolving AI-driven threats.