A newly identified malware known as KadNap is exploiting vulnerabilities in ASUS routers and other edge networking devices to establish a proxy network for cybercriminal activities. Since its emergence in August 2025, KadNap has compromised approximately 14,000 devices, facilitating a decentralized peer-to-peer network that connects to a command-and-control (C2) infrastructure via a modified version of the Kademlia Distributed Hash Table (DHT) protocol.
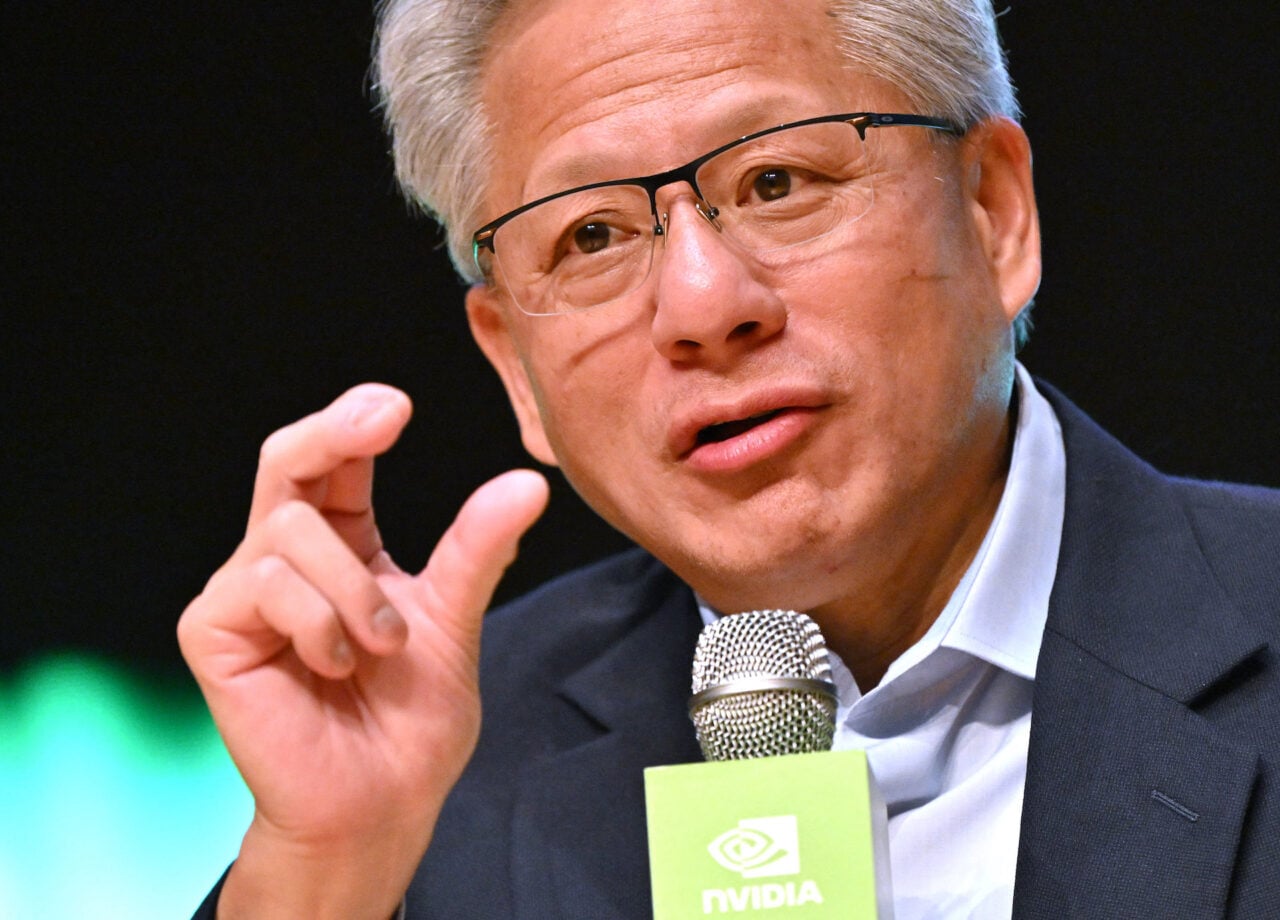
The decentralized nature of KadNap complicates efforts to identify and dismantle its control servers. According to researchers at Black Lotus Labs, the threat research division of Lumen Technologies, close to half of the KadNap network is linked to C2 infrastructure specifically targeting ASUS devices. The remainder connects to two distinct control servers. The majority of the infected devices are located in the United States, which constitutes around 60% of the total, followed by notable numbers in Taiwan, Hong Kong, and Russia.
The infection process begins when a vulnerable device downloads a malicious script named aic.sh from the IP address 212.104.141[.]140. This script establishes a persistent connection using a cron job that executes every 55 minutes. The payload, an ELF binary called kad, installs the KadNap client. Once operational, the malware identifies the host’s external IP address and queries multiple Network Time Protocol (NTP) servers to fetch the current time and system uptime.
KadNap enhances its resilience against takedowns through its customized Kademlia-based DHT protocol, designed to obscure the IP addresses of its infrastructure within a peer-to-peer system. As noted by the researchers, “KadNap employs a custom version of the Kademlia Distributed Hash Table (DHT) protocol, which is used to conceal the IP address of their infrastructure within a peer-to-peer system to evade traditional network monitoring.” This approach makes it challenging for cybersecurity experts to pinpoint and neutralize the C2 servers.
Despite this complexity, Black Lotus Labs has discovered that KadNap’s implementation of Kademlia is somewhat flawed. The botnet maintains a consistent connection to two specific nodes before linking to the C2 servers, thereby reducing the level of decentralization that could otherwise enhance its stealth.
The KadNap botnet is believed to be associated with the Doppelganger proxy service, which is thought to be a rebranding of the Faceless service. This service has previously been linked to the TheMoon malware botnet, which also targeted ASUS routers. Doppelganger offers access to infected devices as residential proxies, enabling the facilitation of malicious traffic, creation of pseudonymization layers, and evasion of security blocklists. These proxies are commonly employed in distributed denial-of-service (DDoS) attacks, credential stuffing, and brute-force attacks, all of which ultimately impact KadNap’s victims.
In response to the threat posed by the KadNap botnet, Lumen Technologies has taken proactive steps to mitigate its impact. At the time of this report, the company announced that it had successfully blocked all network traffic to and from the botnet’s control infrastructure. While this disruption is currently limited to Lumen’s network, the company plans to release a list of indicators of compromise to assist other organizations in combating the botnet effectively.